overleaf template galleryCommunity articles — Recent
Papers, presentations, reports and more, written in LaTeX and published by our community.
Thesis presentation created using the Beamer arrows template from TeXample.net

Reseña del Autor del premio Nobel

Trabajo Herramientas.
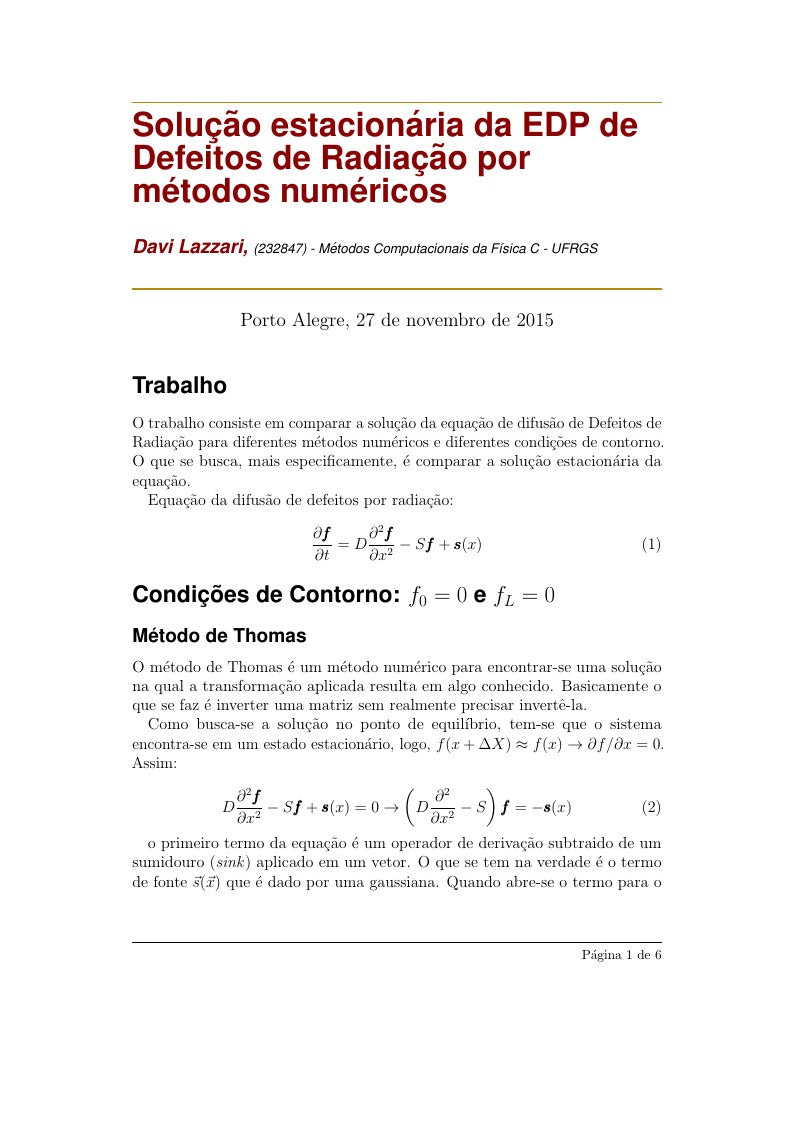
It's a work that discuss solutions of an specific equation using different numerical methods.
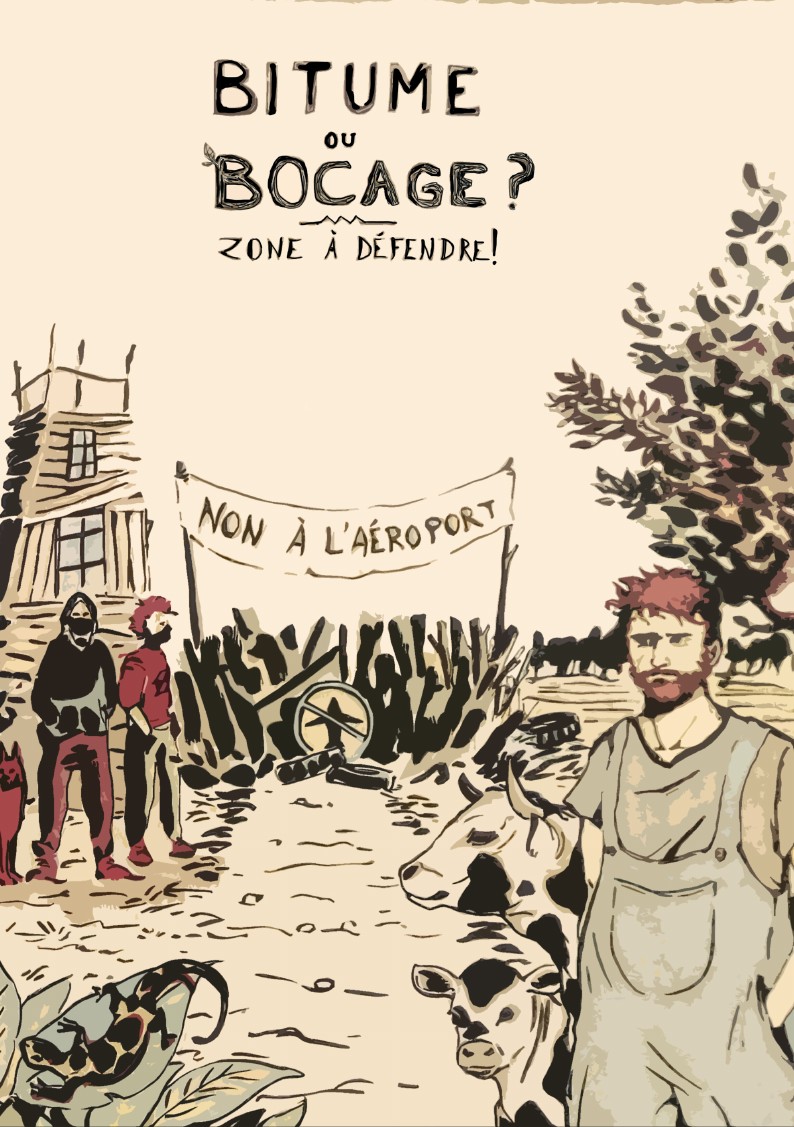
Ce livret retrace l'histoire de la lutte contre le projet de l'aéroport international du Grand Ouest, à Notre-Dame-Des-Landes à une vingtaine de kilomètres au nord de Nantes, en apportant des arguments pour expliquer les raisons d'être et les motivations du mouvement de la résistance. Il est rédigé à l'origine pour accompagner le jeu de plateau coopératif "Zone à Défendre" .
Breve crónica sobre la visita a la imprenta patriótica del Instituto Caro y Cuervo por parte de la universidad Pedagógica Nacional.
En la actualidad, el estudio y análisis de los sistemas de control automático representan un campo de aplicación bastante extendido, esto debido a las imperantes necesidades por mejorar los procesos productivos, optimizar los recursos e incluso para predecir comportamientos, desde entornos educativos, investigativos o industriales, hasta entornos económicos, sociales y demás. En efecto, esto ha impulsado a los desarrolladores a buscar herramientas o alternativas que permitan aumentar las capacidades de cómputo al momento de desarrollar un sistema de control automático. Ahora bien, la instrumentación industrial desde hace muchos años viene comandada por los Autómatas Programables (PLC), dispositivos útiles e ideales para ejecutar las tareas de control de una planta, independientemente de la escala. El presente documento presenta el diseño e implementación de un controlador PID en una planta didáctica conformada con equipos industriales, haciendo uso de OPC y algunos conceptos de la teoría de control. Mediante la herramienta computacional MATLAB se realiza la identificación de la planta obteniendo su función de transferencia, y haciendo uso de algunas herramientas disponibles en este software, se determinan los parámetros de sintonía de un controlador tipo PID, para posteriormente sintonizar la estrategia de control implementada en un autómata programable de gama alta.
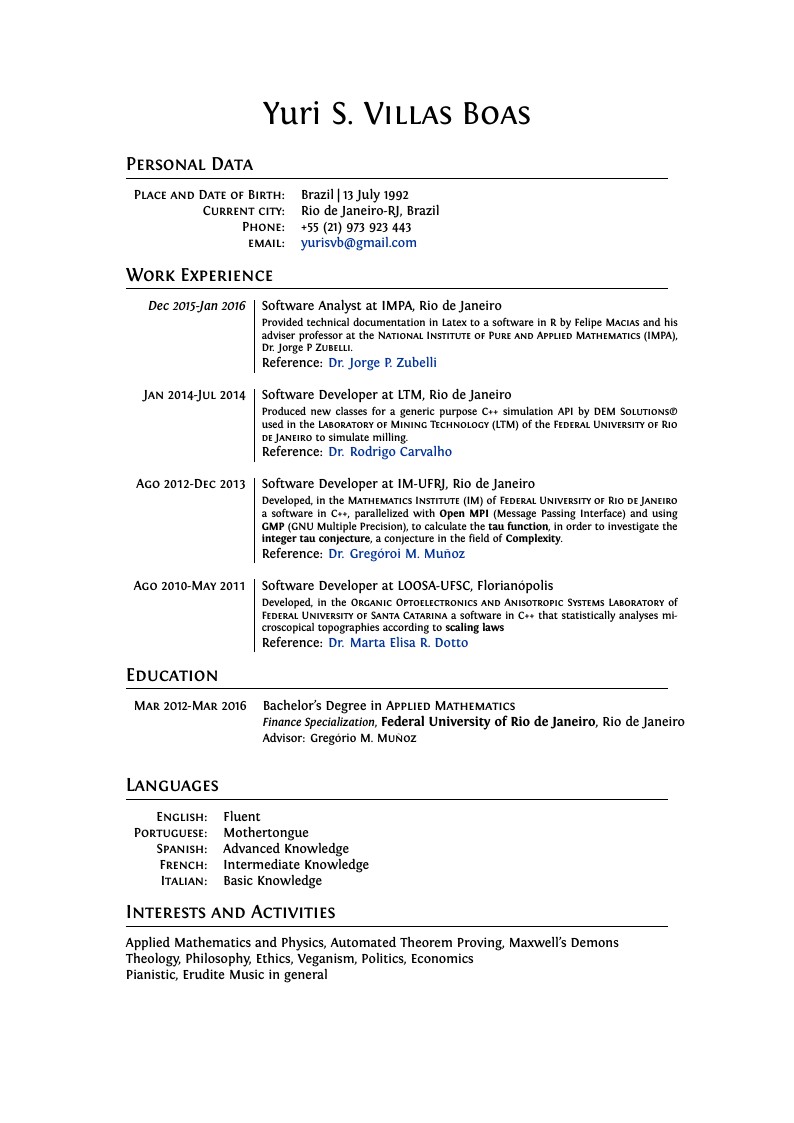
Curriculum Vitae of Yuri da Silva Villas Boas An Applied Mathematics Bachelors by the Federal University of Rio de Janeiro, with expertise in Finance and considerable experience in C++ searches for a position as IT.
\begin
Discover why over 25 million people worldwide trust Overleaf with their work.