LaTeX templates and examples — Two-column
Recent
Modelo para Elaboração de Artigos Científicos da Pós Graduação 2021
Template for initial and final manuscript for the Hawaii International Conference on System Sciences (HICSS).

Homework Assignment Article LaTeX Template Version 1.3.1 (ECL) (08/08/17)
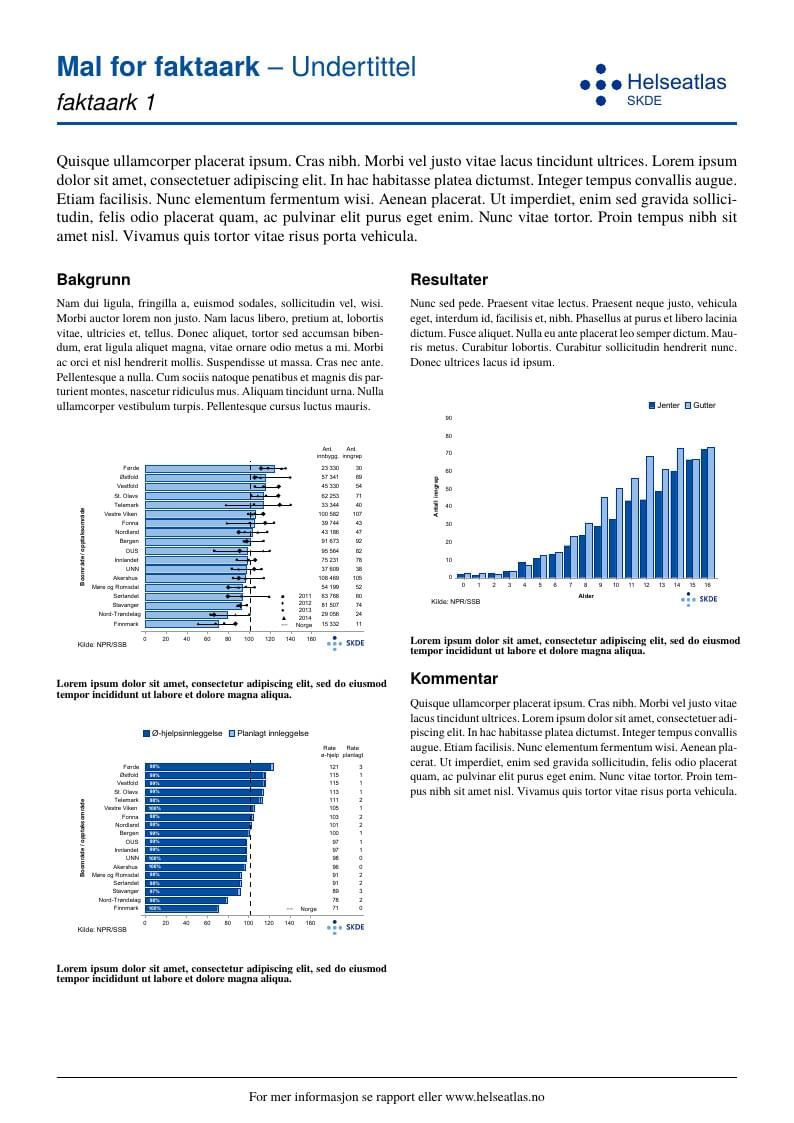
Template for 'Helseatlas' fact sheets, for SKDE Can be both one-page and two-page fact sheets Jan. 29 2019: Simplified setup Sept. 21 2018: New framework (all fact sheets in one document) Apr. 10 2017: LuaLaTeX and TeX Gyre fonts

We all have a good reason to learn a new language; discovering our roots, passion for travel, academic purposes, pure interest etc. However most of us find it hard to become conversationally fluent in a new language while we use traditional resources for learning like textbooks and tutorials on the internet. In this paper we propose a novel approach to learn a new language. We aim to develop an intelligent browser extension, LanGauger, that will help users learn foreign languages. This application will allow users to look up words while they are browsing, by highlighting the text to be learned. The application will then provide a translation of the word, its pronunciation and its usage context in sentences. In addition, this intelligent tutor will also remember what words have been seen by the user, and quiz them on these words at appropriate times. While testing the recall of the user, this feature will also allow users to frequently think about the language and use it.

Cet article étudie deux méthodes utilisées dans le cadre du transport humanitaire en cas de crise (désastre, épidémie...). Le Covering Tour Problem se focalise sur l'équité de distribution des vivres, alors que le Capacitated Vehicle Routing Problem se concentre sur l'urgence de la distribution. Nous proposons une nouvelle approche mélangeant ces deux approches pour former une solution à la fois équitable et rapide. Ce article a été rédigé dans le cadre du TER 2014-2015.
Modelo de TCC para alunos do Programa de Pós-Graduação em Engenharia Clínica e Engenharia Biomédica
Modelo de TCC para alunos do Programa de Pós-Graduação em Redes e Sistemas de Telecomunicações
Modelo de TCC para alunos da graduação dos cursos que utilizam artigos científicos.
\begin
Discover why over 25 million people worldwide trust Overleaf with their work.